-
How to Use Hidden Browser Window Controls
[ad_1] ChromeOS users, learn how to use these hidden browser window controls, and find out why you’ll want to use…
Read More » -

New SecuriDropper Malware Bypasses Android 13 Restrictions, Disguised as Legitimate Applications
[ad_1] A new malware is bypassing an Android 13 security measure that restricts permissions to apps downloaded out of the…
Read More » -

Top Tech Conferences & Events to Add to Your Calendar in 2023
[ad_1] Looking for a list of the top tech conferences and events in 2023? Explore our guide to find out…
Read More » -

Google Offers Bug Bounties for Generative AI Security Vulnerabilities
[ad_1] Google’s Vulnerability Reward Program offers up to $31,337 for discovering potential hazards. Google joins OpenAI and Microsoft in rewarding…
Read More » -

Inside the Canvas: Exploring the Top 5 Questions About AI Art
[ad_1] Learn how AI algorithms are used to create unique works of art, from abstract images to intricate designs, and…
Read More » -

Which Is Best in 2023?
[ad_1] Feature Amazon Web Services Google Cloud Containers Docker and Kubernetes Kubernetes Virtual machines Yes Yes Load balancing services Yes…
Read More » -
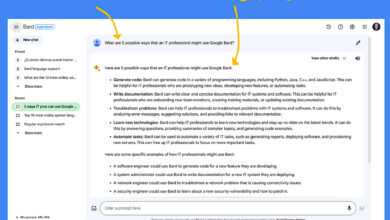
How to Use Google Bard (2023): A Comprehensive Guide
[ad_1] Bard is Google’s public entry into the highly competitive field of artificial intelligence chatbots, which also includes OpenAI’s ChatGPT.…
Read More » -
What Is Google Bard, and How Does It Work?
[ad_1] Bard is Google’s artificial intelligence chatbot that generates responses to user-provided natural language prompts. In response to a prompt,…
Read More » -

EqualAI Releases 11 Principles for Responsible AI Governance
[ad_1] Stakeholders from underrepresented groups should be involved in the integration of AI into business processes or functions. The nonprofit…
Read More » -

New DDoS Attack is Record Breaking: HTTP/2 Rapid Reset Zero-Day Reported by Google, AWS & Cloudflare
[ad_1] A vulnerability in the HTTP/2 network protocol is currently being exploited, resulting in the largest DDoS attack in history.…
Read More »