For Data Breaches, Cloud Assets are Biggest Cybersecurity Headache

[ad_1]
Thales cloud security study shows that 79% of organizations have more than one cloud provider and 75% of companies said they store at least 40% of their sensitive data in the cloud.

While Thales, in its 2023 Cloud Security Study, found that well over a third (39%) of businesses experienced a data breach in their cloud environment last year versus 34% in 2021, organizations are increasingly caching sensitive data in multiple cloud environments.
In the report, based on a survey of 3,000 IT and security teams across 18 countries in EMEA, the Americas and Asia Pacific:
- Seventy-five percent of IT executives classified as sensitive more than 40% of their data stored in the cloud, compared to 49% this time last year.
- Thirty-eight percent of respondents said software as a service applications are the main target for hackers, followed by cloud-based storage (36%).
Multicloud causing operational complexity
The study shows how more companies are using more cloud service providers, tracking with the 35% growth in the number of reported providers in the market. The study authors noted that the average number of cloud infrastructure providers is now 2.3, and that more than three-quarters (79%) of this year’s respondents have more than one cloud provider (Figure A).
Figure A
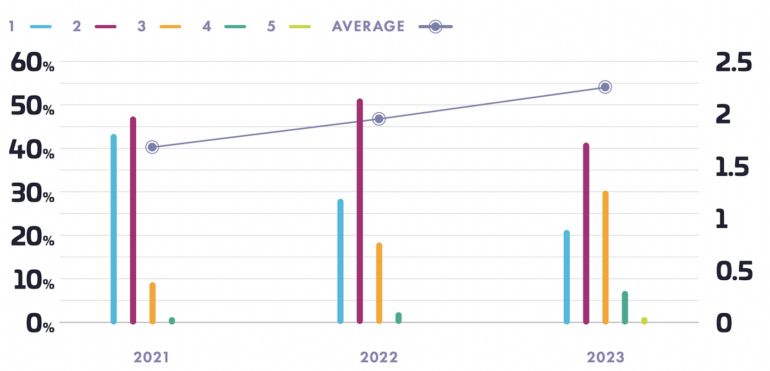
“With a larger number of platforms to secure, the opportunity for operational errors grows, increasing the attack surface with each error. Organizations either have to dedicate separate teams to specialize in each platform or expect their security teams to become well-versed in multiple platforms at the same time,” according to the study.
More sensitive data being stored in the cloud
The study reported that organizations are lifting more workloads and data into the cloud: The number of organizations that reported that 60% or more of their workloads are in the cloud increased from 23% to 27% year over year.
SEE: Read how IBM is boosting cloud data practice (TechRepublic)
The report polled respondents two ways about sensitive data in the cloud to determine how they are deploying their data and saw increases in both directions. The survey asked about:
- The percentage of an organization’s total sensitive data that is stored in the cloud.
- The percentage of all of the data an organization stores in the cloud that is sensitive.
It found that:
- In last year’s study, 52% of respondents said that more than 40% of their sensitive data was in the cloud. This year, that amount increased to 64%.
- The number of respondents who said that 40% or more of their data stored in the cloud is sensitive data, increased from 49% in last year’s study, to 75% this year.
Encryption is increasing, but slowly
In this year’s study, 22% of respondents said that over 60% of their sensitive data in the cloud is encrypted and 40% said over half of that cloud-based sensitive data is encrypted. Those numbers constitute an improvement from last year’s study, which reported that only 17% of respondents had said over half of their sensitive data in the cloud was encrypted. That said, only 2% said 100% of their sensitive data in the cloud is encrypted (Figure B).
Figure B
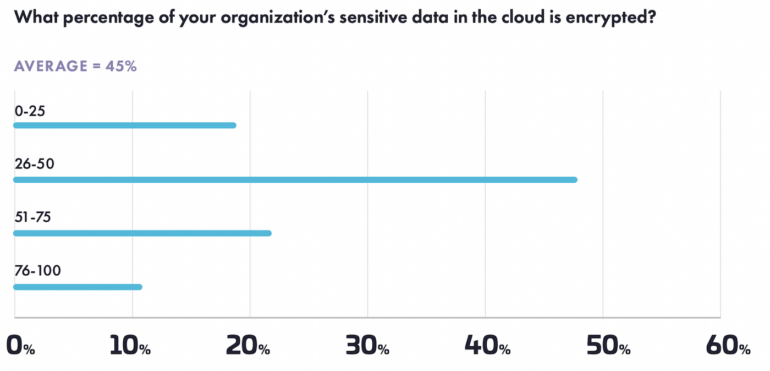
Additionally, 62% of IT executives who responded to the survey said they have five or more key management systems, which Thales said constitutes increased complexity for securing sensitive data.
Software-as-a-service creating security challenges
Not only do most companies report having multiple cloud service providers, the rise in the use of SaaS apps is expanding the threat surface for data exfiltration:
- In the 2022 study, 16% of respondents reported their enterprises deployed 51-100 different SaaS applications.
- In this year’s study, that proportion grew to 22% of respondents, and 55% (versus 46% in the prior year) noted that managing data in the cloud is more complex than in on-premise environments.
- Additionally, 83% expressed concerns over data sovereignty, with 55% of respondents asserting that data privacy and compliance in the cloud has become more difficult.
The study included a ranking question on which attack targets are most likely to be attacked. SaaS was mentioned first by 38% of respondents, followed by cloud storage at 36% of those polled. Additionally, the study’s authors said the number of survey respondents reporting a data breach during the study period was up 4% from last year’s report — 35% to 39%.
Data breaches and human error
Over half (55%) of respondents to the survey said human error triggered cloud data breaches at their organizations, but only 41% of organizations have implemented zero-trust controls in their cloud infrastructure — only 38% use zero-trust protocols in their cloud networks. However, more companies are adopting authentication protocols for employees: 65% of respondents to Thales’ survey said they now deploy multifactor authentication.
SEE: Palo Alto Networks on differently about cloud security (TechRepublic)
“Organizations are operating in a dynamic multi-cloud landscape, demanding seamless and efficient security measures,” said Sebastien Cano, senior vice president for cloud protection and licensing activities at Thales.
“To overcome challenges arising from human error and misconfiguration, it is imperative that data protections in the cloud are simplified and easily manageable.” He said that the key to enhancing cloud security lies in treating cloud environments as an extension of existing infrastructure. “By adopting this approach, organizations can effectively bolster security and ensure comprehensive protection across the entire digital ecosystem.”
[ad_2]
Source Credit