Proofpoint Exposes Sophisticated Social Engineering Attack on Recruiters That Infects Their Computers With Malware

[ad_1]
Recruiters and anyone else involved in hiring processes should be knowledgeable about this social engineering attack threat.
A new report from U.S.-based cybersecurity company Proofpoint exposes a new attack campaign operated by a financially-oriented threat actor dubbed TA4557 with high financial data theft risks and possibly more risks such as intellectual property theft.
In this social engineering campaign, the threat actor targets recruiters with benign content before infecting their machines with the More_Eggs malware. This threat actor takes extra care to avoid being detected.
Jump to:
How recruiters are targeted by threat actor TA4557
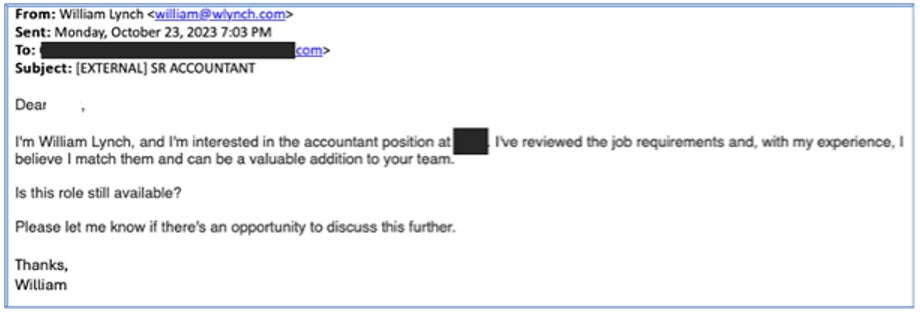
The latest attack campaign from threat actor TA4557, as exposed by Proofpoint, targets recruiters by sending them a direct email. The group pretends to be an individual interested in a job (Figure A).
Figure A
The email does not include any malicious content. Once the recruiter replies to the email, the attacker replies with a link leading to an attacker-controlled website posing as an individual’s resume (Figure B).
Figure B
An alternative method used by the threat actor consists of replying to the recruiter with a PDF or Microsoft Office Word file containing instructions to visit the fake resume website.
Infection leads to More_Eggs malware
The website employs filtering mechanisms to assess whether the subsequent phase of the attack should be initiated. If the criteria for filtering are not met, the user is presented with a plain text resume. If the filtering checks are successfully passed, the user is redirected to the candidate website, where they are prompted to solve a CAPTCHA.
Upon successful completion, the user is provided with a ZIP file that includes a Microsoft Windows shortcut (LNK) file. If executed, the LNK file abuses a legitimate software ie4uinit.exe to download and run a scriptlet from a location stored in the ie4uinit.inf file. The technique known as Living Off The Land consists of using existing legitimate software and tools to accomplish malicious actions on the system, which minimizes the likelihood of being detected.
The downloaded scriptlet decrypts and drops a DLL file before attempting to create a new process to execute the DLL by using Windows Management Instrumentation. If it fails, the scriptlet tries another approach by using the ActiveX Object Run method.
Once the DLL is executed, it decrypts the More_Eggs malware along with the legitimate MSXSL executable. Then, it initiates the creation of the MSXSL process using the WMI service. The DLL deletes itself once the infecting process is done.
According to Proofpoint, More_Eggs is a malware that enables persistence and profiling of the infected system; it is also often used to download additional payloads.
A discreet yet efficient threat actor
TA4557 employs various strategies to evade detection and maintain a low profile, demonstrating a commitment to staying below the radar.
In other attack campaigns, mostly in 2022 and 2023, the threat actor used a different technique that mainly consisted of applying for open positions on job offer websites. The threat actor used malicious URLs or files containing malicious URLs in the application, but the URLs were not hyperlinked, meaning the recipient had to copy and paste the URLs directly into their browser. That technique is interesting because the use of such a link will likely not trigger as many security alarms. According to Proofpoint researchers, TA4557 still uses that technique in parallel with the newly reported technique.
In addition, the threat actor previously created fake LinkedIn profiles, pretending to be a recruiter and reaching out to people looking for a job.
The use of LOTL techniques is an indication that the threat actor tries to stay discreet and undetected.
The DLL file used by the threat actor employs anti-sandbox and anti-analysis techniques, such as incorporating a loop strategically crafted to extend the execution time while slowly retrieving the RC4 key needed to decipher the More_Eggs backdoor. Multiple checks are also done to see if the code is running in a sandbox or in a debugging environment. Once the infection process has gone through, the DLL deletes itself to remove evidence of its presence and render incident analysis harder.
TA4557 is described by Proofpoint as a “skilled, financially motivated threat actor” who demonstrates sophistical social engineering. The group regularly changes its sender emails, fake resume domains and infrastructure. Proofpoint believes the same threat actor targeted anti-money laundering officers at U.S. credit unions in 2019.
From a global point of view, the researchers noticed an increase in threat actors engaging their targets using benign content first to build confidence during the interaction before sharing harmful content.
How to protect from this malware threat
TA4557 uses social engineering to infect the machines of unsuspecting victims, which are recruiters in this attack campaign; in the past, the threat actor also targeted individuals looking for jobs. So, it is advised to educate all people involved in hiring processes about these kinds of social engineering techniques.
It is recommended never to open a document or click on a link that seems suspicious. When in doubt, employees must alert their IT department and have the documents or links analyzed.
Security solutions must be deployed on all endpoints, and alerts should be carefully analyzed.
Email content should be analyzed by security solutions capable of detecting anomalies instead of only URLs or attached files to try to detect social engineering-based campaigns.
All operating systems and software must be kept up to date and patched to avoid being compromised by common vulnerabilities.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.
[ad_2]
Source Credit




